Enough best practices.
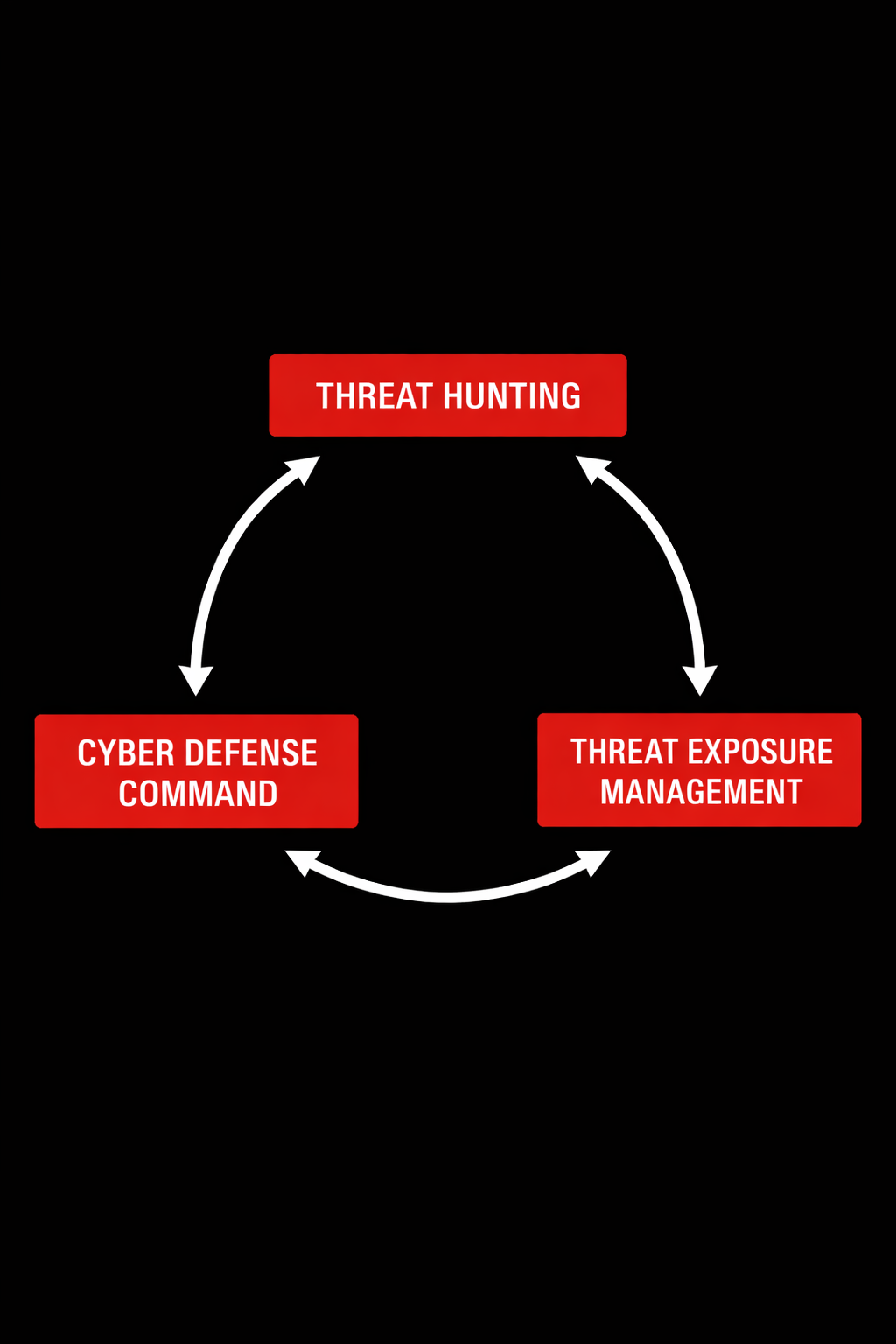
We build and refine cyber defense measures through Threat Hunting, Threat Exposure Management, and Cyber Defense Command.
Our work includes hypothesis-driven compromise assessments, exposure workflow definitions, and reinforcement of leadership decisions in high-stakes scenarios.
Outcomes include evidence-based statements of compromise, prioritized remediation roadmaps, defined ownership models, and defensible courses of action grounded in threat context and execution reality.
NO HACKS, JUST HUNTS
Time for better outcomes.
Threat
Hunting
Compromise Assessments & Proactive Investigations
-
Detection programs react by design. They reveal only what you have already modeled.
Our engagements search for adversary behavior that has not triggered alerts.
-
We define hypotheses specific to how an attacker operates in your environment.
Each hypothesis becomes a technical question that requires evidence, not opinion.
We validate those hypotheses against your identity, endpoint, email, and network telemetry.
Our hunts use your tools, on-prem and cloud, or perform dedicated data collection.
When telemetry does not allow a conclusion, we identify the gap and explain its impact.
-
✔ Statement on whether evidence of compromise exists, with an executive summary.
✔ Identified attack paths and affected systems.
✔ Prioritized response actions based on observed compromise.
✔ Detected visibility gaps, their operational impact, and how to address them.
✔ For recurring collaboration, tracked detection improvements over time.
Threat
Exposure
Management
Threat-Informed Decision Reinforcement
-
Cyber defense decisions shape your outcomes before, during, and after the incident.
Our engagements operate alongside leadership, reinforcing judgment without replacing authority.
-
We work within a specific decision context to confirm mutual fit before recurring collaborations.
Scenarios include crisis coordination, leadership transitions, and mergers & acquisitions.
We translate the operational reality into threat-informed decisions at the leadership table, adjusted to your risk tolerance and backed by our expertise and technical clarity.
When the stakes are high, we cut through complexity to define the course of action.
-
✔ Defined course of action, considering indirect and long-term consequences.
✔ Reliable, effective decisions in high-stakes situations.
✔ Cyber defense realities anchored to the leadership’s risk tolerance.
✔ Defensible positioning grounded in documented rationale.
✔ For recurring collaboration, tracked decision discipline over time.
Cyber
Defense
Command
Vulnerability Management & CTEM Workflows
-
VM programs focus on metrics but fail to reduce exposure. CTEM initiatives drift toward compliance reporting.
Our engagements examine how your VM and CTEM workflows operate in practice and where relevant findings go unactioned.
-
We examine asset and identity scoping, finding validation, and remediation effectiveness.
Our focus is on mobilization. Prioritized findings only matter if they lead to changes.
We work with you to define the exposure management workflows and drive their implementation.
When continuous execution stalls, we identify and remove the constraint.
-
✔ Roadmap to implement or evolve your VM and CTEM initiatives.
✔ Tailored exposure management workflows with mobilization at the core.
✔ Defined ownership and accountability model to support decision-making.
✔ Prioritized remediation criteria to facilitate changes.
✔ For recurring collaboration, tracked exposure reduction over time.
WHEN THE RUBBER MEETS THE ROAD
